05
JunJava Technical Architect Interview Questions & Answers
In this tutorial, you will find Top 50 Java Technical Architect Interview questions and answers explained thoroughly. And if you want to learn Java programming for free, enroll in our Java Online Course Free With Certificate and build real coding skills that matter.
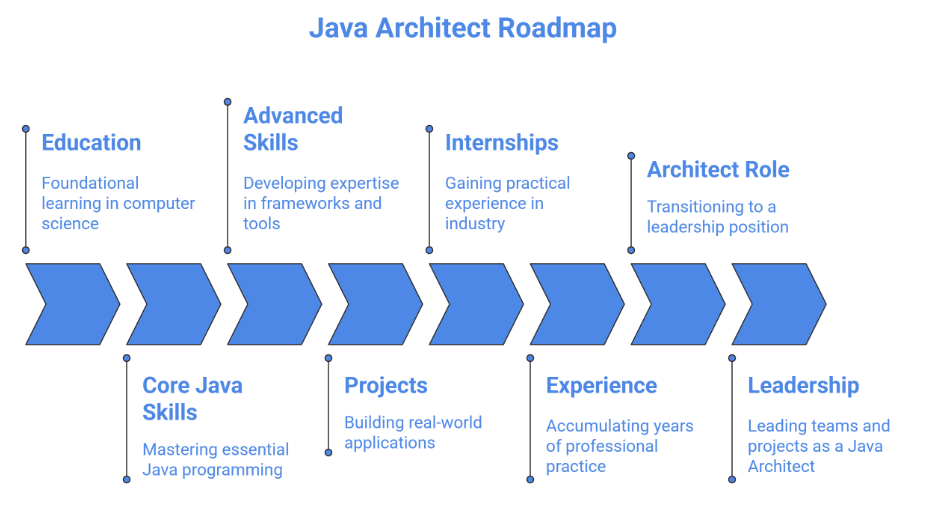
What is a Java Technical Architect?
A Java Technical Architect is a senior-level professional responsible for designing, planning, and overseeing the implementation of Java-based enterprise applications. They bridge the gap between business requirements and technical solutions, ensuring that software systems are scalable, maintainable, secure, and high-performing.
Java Technical Architect Interview Questions for Freshers
1. What is functional programming in Java, and how was it introduced?
Functional programming in Java is a programming paradigm that treats computation as the evaluation of mathematical functions and avoids changing state or mutable data. It emphasizes immutability, higher-order functions, and declarative code.
In Java, functional programming was formally introduced with Java 8 through lambda expressions, functional interfaces (like Function, Predicate, Consumer), and the Stream API. These features allow developers to write more concise, readable, and maintainable code by focusing on what to do rather than how to do it.
2. Why use the Spring framework in Java applications?
The Spring Framework is widely used in Java applications because it simplifies enterprise application development by providing comprehensive infrastructure support. Key reasons include:
- Spring promotes loose coupling by allowing objects to be created and injected by the framework rather than manually, improving maintainability and testability.
- Spring is modular, so developers can use only the parts they need (e.g., Spring MVC, Spring Data, Spring Security) without including the whole framework.
- Spring enables separation of cross-cutting concerns like logging, security, and transaction management.
- It provides built-in support for database access (JDBC, JPA/Hibernate), messaging (JMS), and web services (REST/SOAP).
- Spring applications are easy to scale, test, and deploy in enterprise environments, supporting microservices and cloud-native architectures.
3. What are design patterns in Java, and why are they important?
Design patterns in Java are effective, reusable solutions to common software design problems. They offer templates for addressing issues tied to object creation, organization, and interaction in a consistent and efficient way.
Importance of Design Patterns:
- Reusability: They let developers use standard solutions instead of reinventing the wheel.
- Maintainability: Well-structured patterns make code easier to read, maintain, and expand.
- Scalability: Patterns offer flexible structures that can manage changes and increasing application complexity.
- Communication: Using design patterns creates a common language among developers, such as Singleton, Factory, and Observer.
- Best Practices: Patterns represent industry best practices and assist in building strong and efficient software.
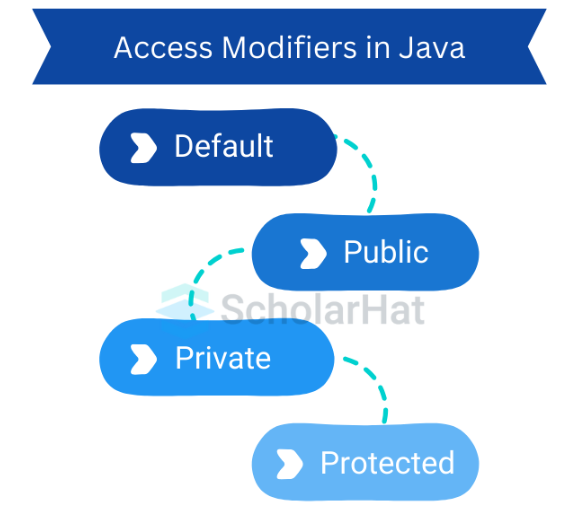
4. Explain Access Modifiers in Java.
Access Modifiersin Java define the visibility or accessibility of classes, methods, and variables. They control which parts of the program can access a particular member. Java provides four main access specifiers:
- private : Accessible only within the same class, used to hide data from other classes.
- default (no modifier): Accessible within the same package, no modifier is specified.
- protected: Accessible within the same package and by subclasses in other packages.
- public: Accessible from any class anywhere, globally visible.
5. What is data encapsulation, and why is it important?
Data encapsulation in Java is the process of wrapping the data (variables) and methods that operate on the data into a single unit (class) and restricting direct access to some of the object’s components using access specifiers like private.
It is important for the following reasons:
- Data Hiding: Protects the internal state of an object from unauthorized access or modification.
- Control: Provides control over how the data is accessed or modified via getter and setter methods.
- Maintainability: Makes the code easier to maintain and modify without affecting other parts of the program.
- Security: Helps prevent accidental or malicious corruption of data.
6. How do you avoid database deadlocks in Java?
A database deadlock occurs when two or more transactions block each other by holding locks on resources that the others need, causing the system to halt. Avoiding deadlocks in Java requires careful design and transaction management.
Here are three key ways to avoid database deadlocks in Java:
- Access Resources in a Consistent Order: Always acquire multiple database locks in the same order across different transactions to prevent circular waiting.
- Keep Transactions Short and Simple:Minimize the time a transaction holds locks by committing or rolling back quickly. This reduces the chance of conflict.
- Use Appropriate Isolation Levels: Choose a lower isolation level, like READ_COMMITTED, when possible. Avoid unnecessary locking to reduce contention.
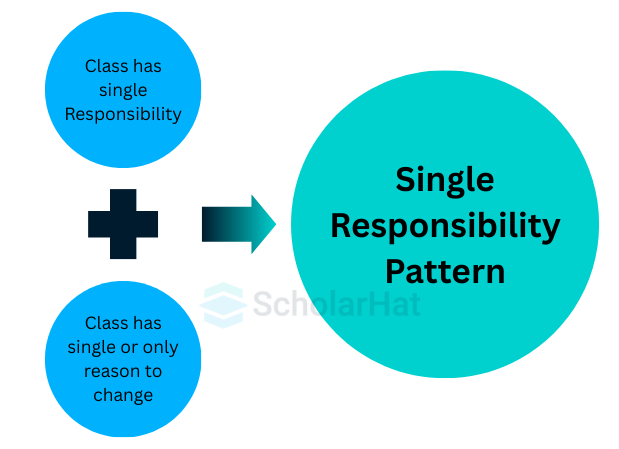
7. What is SOLID in software architecture?
SOLID is a set of five design principles in object-oriented software architecture aimed at making software more maintainable, flexible, and scalable. Each letter stands for a principle:
- S – Single Responsibility Principle (SRP):A class should have only one reason to change. This means it should focus on a single responsibility or function.
- O – Open/Closed Principle (OCP):Software entities (classes, modules, functions) should be open for extension but closed for modification. This allows for new features without changing the existing code.
- L – Liskov Substitution Principle (LSP):Subtypes must be replaceable with their base types without affecting the program's correctness.
- I – Interface Segregation Principle (ISP):Clients should not have to rely on interfaces they do not use. It is better to have small, specific interfaces instead of large, general ones.
- D – Dependency Inversion Principle (DIP): High-level modules should not rely on low-level modules. Both should depend on abstractions (interfaces), which reduces tight coupling.
8. Differentiate between interface and abstract class in Java.
| Feature | Interface | Abstract Class |
| Purpose | Defines a contract that implementing classes must follow. | Provides a base class with partial implementation that subclasses can extend. |
| Methods | By default, methods are abstract (Java 7/8 onwards can have default and static methods). | Can have abstract and concrete methods. |
| Fields | Can only have public static final constants. | Can have instance variables and constants of any access modifier. |
| Multiple Inheritance | Supports multiple inheritance (a class can implement multiple interfaces). | Does not support multiple inheritance; a class can extend only one abstract class. |
| Constructors | Cannot have constructors. | Can have constructors. |
| Use Case | When unrelated classes need to share a contract. | When classes share common behavior and structure. |
9. What is JDBC in Java?
JDBC (Java Database Connectivity) is a Java API that allows Java applications to work with relational databases. It offers a standard way to connect to databases, execute SQL queries, and get results.
10. What is Hibernate in Java?
Hibernate is a popular Object-Relational Mapping (ORM) framework in Java that simplifies database operations by mapping Java objects to database tables. It eliminates the need to write complex SQL queries and handles database interactions automatically.
11. Why prefer Hibernate over JDBC?
While JDBC provides a low-level API to interact with databases in Java, Hibernate offers a higher-level, more efficient, and object-oriented approach. Here’s why Hibernate is often preferred over plain JDBC:
- Object-Relational Mapping (ORM):Hibernate maps Java objects directly to database tables, eliminating manual conversion between objects and relational data.
- Less Boilerplate Code: With JDBC, developers write repetitive code for connection handling, statements, and result sets. Hibernate automates this, reducing boilerplate.
- Database Independence: Hibernate abstracts SQL differences, making it easier to switch databases without changing code.
- Automatic SQL Generation: Hibernate generates optimized SQL queries automatically, reducing chances of errors.
12. What is Remote Procedure Call (RPC) in Java?
A Remote Procedure Call (RPC) in Java is a mechanism that allows a program to invoke methods or procedures on a remote system (server) as if they were local, abstracting the details of network communication. RPC enables distributed computing by letting different applications or services communicate over a network.
13. Differentiate SOAP vs. REST services.
| Feature | SOAP | REST |
| Protocol | Protocol-based, uses XML for messages. | Architectural style, can use multiple formats (JSON, XML, plain text). |
| Transport | Primarily HTTP, but can use SMTP, TCP, etc. | Mainly HTTP (GET, POST, PUT, DELETE). |
| Message Format | Strict XML format with WSDL (Web Services Description Language). | Flexible; supports JSON, XML, HTML, or plain text. |
| Standards | Built-in standards for security (WS-Security), transactions, reliability. | Relies on underlying HTTP standards for security (HTTPS) and statelessness |
| Performance | Slower due to verbose XML and additional processing. | Faster due to lightweight formats like JSON. |
| State | Can be stateful or stateless. | Stateless; each request contains all necessary information. |
| Error Handling | Built-in error handling via SOAP fault. | Uses standard HTTP status codes for errors. |
| Use Case | Enterprise applications requiring high security and ACID transactions. | Web/mobile apps requiring scalability, performance, and simplicity. |
14. What is Java Architecture?
Java Architecture refers to the design and structure of the Java platform that allows Java programs to be platform-independent, secure, and robust. It defines how Java code is compiled, executed, and interacts with hardware and software components.
Key Components of Java Architecture:
- JDK provides tools for developing Java applications, including the compiler (javac), debugger, and libraries.
- JRE contains the Java Virtual Machine (JVM), core libraries, and other components needed to run Java programs.
- JVM converts Java bytecode into machine code. It provides platform independence, security, and memory management.
- Java API are pre-built classes and packages that simplify development (e.g., java.util, java.io, java.net).
15. Explain Sharding and its benefits.
Sharding is a database architecture pattern where a large database is horizontally partitioned into smaller, faster, and more manageable pieces called shards. Each shard holds a subset of the data and can be stored on a separate database server. Sharding is commonly used in high-volume Java applications to improve performance and scalability.
- Data is split based on a shard key, such as user ID or region.
- The application or middleware layer routes queries to the correct shard.
- Each shard can operate on its own, which reduces contention and prevents bottlenecks.
Benefits of Sharding:
- Improved Performance:Queries run on smaller datasets, which lowers response time.
- Scalability:You can add more shards as data grows, without impacting existing shards.
- High Availability:If one shard fails, the entire database does not go down; the other shards keep working.
- Efficient Resource Use:It spreads the load across multiple servers, balancing CPU, memory, and storage use.
- Reduced Lock Contention:Since each shard manages a part of the data, concurrent transactions are less likely to conflict.
Java Technical Architect Interview Questions for Intermediate
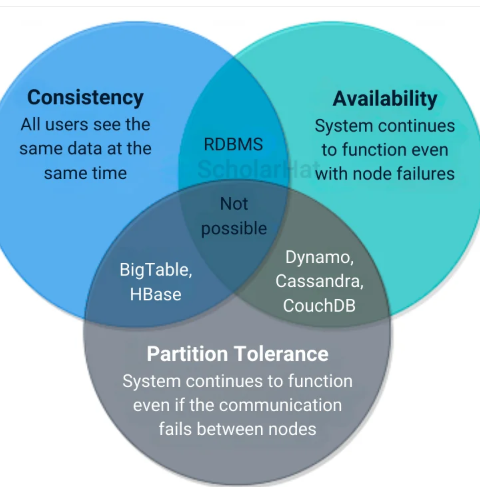
16. Explain the CAP theorem.
The CAP theorem is a fundamental principle in distributed systems, including Java-based enterprise applications. It states that a distributed system can provide only two out of the following three guarantees simultaneously:
- Every read receives the most recent write.
- All nodes see the same data at the same time.
- Every request receives a response, regardless of whether it contains the latest data.
- The system is operational and responsive at all times.
- The system continues to operate even if network partitions or communication failures occur between nodes.
17. How do you ensure security in Java applications?
Ensuring security in Java applications involves implementing multiple layers of protection to safeguard data, prevent unauthorized access, and maintain application integrity. Java provides built-in features, libraries, and best practices to achieve robust security.
Key Measures to Ensure Security:
- Use frameworks like Spring Security or Java EE Security API to manage user login, roles, and access control.
- Implement role-based access control (RBAC) to restrict actions based on user roles.
- Encrypt sensitive data at rest (database) and in transit (network) using protocols like HTTPS, TLS/SSL.
- Use Java libraries such as JCE (Java Cryptography Extension) for encryption and decryption.
- Validate and sanitize all user inputs to prevent SQL Injection, XSS, and command injection attacks.
- Use prepared statements or ORM frameworks like Hibernate to avoid raw SQL queries.
18. How to handle exceptions in Spring MVC?
- @ExceptionHandler for controller-level exceptions.
- @ControllerAdvice for global exception handling.
- @ResponseStatus on custom exceptions for HTTP status.
- Extend ResponseEntityExceptionHandler for REST APIs.
19. What is method overloading in Java?
- Return type alone cannot differentiate overloaded methods.
- It is an example of compile-time polymorphism.
- Improves readability and reusability of code
20. What assets are in a Java product line architecture?
Assets in a Java Product Line Architecture
- Core Assets: Reusable modules, frameworks, and common services.
- Variation Points: Configurations and features that allow customization.
- Domain Models: Requirements, use cases, and UML diagrams.
- Test Assets – Automated test cases and reusable test data.
- Documentation: Standards, guidelines, and API references.
21. Explain cloud computing and its relevance to Java.
Cloud computing is the delivery of computing services (servers, storage, databases, networking, software, analytics, AI, etc.) over the internet (“the cloud”) instead of using local servers or personal devices. It allows organizations to scale resources on demand, reduce costs, and improve flexibility.
Relevance to Java
- Platform Independence – Java runs on the JVM, making it portable across different cloud environments.
- Scalability & Performance – Java frameworks (Spring Boot, Jakarta EE, Micronaut) are widely used to build scalable cloud-native applications.
- Integration with Cloud Services – Java SDKs/APIs support major cloud providers like AWS, Azure, and Google Cloud.
- Microservices Support – Java works seamlessly with microservices and container technologies (Docker, Kubernetes), common in cloud deployments.
- Enterprise Adoption – Most large-scale enterprise apps are built in Java, making it a natural fit for cloud migration.
22. How to optimize database connections in Java?
- Instead of creating a new DB connection for every request, use a pool (e.g., HikariCP, Apache DBCP, C3P0) to reuse existing connections.
- This reduces overhead and improves performance.
- Always close Connection, Statement, and ResultSet objects in a finally block or use try-with-resources.
- Prevents memory leaks and keeps connections available in the pool.
- Prepared statements are precompiled by the DB, so they reduce parsing overhead and improve performance.
- They also help prevent SQL injection.
- When inserting/updating multiple rows, use batch updates instead of executing statements one by one.
- Write efficient SQL queries, use indexes where necessary, and avoid unnecessary joins.
- Fetch only the required columns instead of SELECT *.
23. What is 'Fail Fast' or 'Fail Early' in Java?
24. How to manage sessions in Servlets?
- HttpSession – Server creates a session object per user (most common).
- Cookies – Store session ID or data in the client’s browser.
- URL Rewriting – Append session ID to the URL.
- Hidden Form Fields – Store session data in hidden HTML fields.
25. What is clustering in Java?
- High Availability (HA): If one server goes down, another takes over.
- Load Balancing: Requests are distributed among multiple servers for better performance.
- Scalability: Adding more servers improves handling of high traffic.
26. What is JVM, JRE, and JDK?
- JVM (Java Virtual Machine): Runs Java bytecode on any platform.
- JRE (Java Runtime Environment): JVM + core libraries for running Java applications.
- JDK (Java Development Kit): JRE + development tools like compiler, debugger for building Java applications.
27. What is the Observer pattern in Java?
28. What is dependency injection and how is it used in Spring?
Dependency Injection is a design pattern in which an object receives its dependencies from an external source rather than creating them itself. This promotes loose coupling, testability, and flexibility.
Benefits of DI in Spring
- Promotes loose coupling between classes.
- Makes unit testing easier by allowing mock dependencies.
- Centralizes object configuration in the IoC container.
- Reduces boilerplate code for object creation and wiring.
29. What is the difference between synchronized and ReentrantLock in Java?
- Automatically acquires and releases the lock.
- Cannot interrupt a thread waiting for the lock.
- Does not support fairness policies.
- Simpler to use for basic synchronization.
Example:
public synchronized void increment() {
// critical section
}
- Supports tryLock(), timed lock, and interruptible lock.
- Can implement fairness policy (first-come-first-served).
- Provides better flexibility for advanced concurrency control.
- Must manually release lock in a finally block to avoid deadlocks.
Example:
import java.util.concurrent.locks.ReentrantLock;
ReentrantLock lock = new ReentrantLock();
public void increment() {
lock.lock(); // acquire lock
try {
// critical section
} finally {
lock.unlock(); // release lock
}
}
30. How do you handle memory leaks in Java applications?
A memory leak occurs when objects are no longer needed but still referenced, preventing the garbage collector from reclaiming memory. Over time, this can lead to OutOfMemoryError and degraded performance.
To Handle And Prevent Memory Leaks:
- Use Profiling Tools: Analyze heap usage with tools like VisualVM or JProfiler.
- Avoid Unnecessary References: Nullify objects and remove unused collection entries.
- Use Weak References: Apply WeakReference or SoftReference for caches/listeners.
- Properly Close Resources: Always close streams, sockets, and database connections.
- Avoid Leaks in Collections: Remove obsolete entries from maps, lists, and listener lists.
- Monitor Object Creation: Limit unnecessary creation of large or temporary objects.
- Handle Thread-Local Carefully: Remove thread-local variables when no longer needed.
Advanced Java Technical Architect Interview Questions
31. Explain Single Responsibility Principle (SRP).
Single Responsibility Principle (SRP) is one of the core SOLID principles in software design. It states that a class should have only one reason to change, meaning it should be focused on a single functionality or responsibility. When a class has multiple responsibilities, changes in one functionality may impact other unrelated parts of the code, making maintenance difficult and increasing the chance of bugs.
- It makes code easier to understand and maintain.
- It reduces coupling between different parts of a program.
- It helps in testing and debugging, since each class does only one thing
Example:
// Bad: Multiple responsibilities
class Employee {
void calculateSalary() { /*...*/ } // Payroll
void saveToDatabase() { /*...*/ } // Persistence
}
// Good: Single Responsibility
class Payroll {
void calculateSalary() { /*...*/ }
}
class EmployeeRepository {
void save(Employee emp) { /*...*/ }
}Here, Payroll handles salary calculation, and EmployeeRepository handles data persistence—each has a single responsibility.
32. What is the role of 'throw' and 'throws' in Java?
- Used inside a method to actually throw an exception.
- Throws a single exception object.
- Immediately stops the execution of the current method.
- Declared in a method signature to indicate that the method might throw one or more exceptions.
- Doesn’t throw the exception itself; informs the caller to handle it.
- Can specify multiple exceptions separated by commas.
| Feature | throw | throws |
| Purpose | Actually throws an exception | Declares that a method may throw an exception |
| Location | Inside method body | In method signature |
| Number | Single exception object | One or more exception types |
33. What is JWT? Explain JWT Authentication process.
JWT (JSON Web Token) is a compact, URL-safe token used for securely transmitting information between parties as a JSON object. It is widely used for authentication and authorization in web applications.
JWT Authentication process:
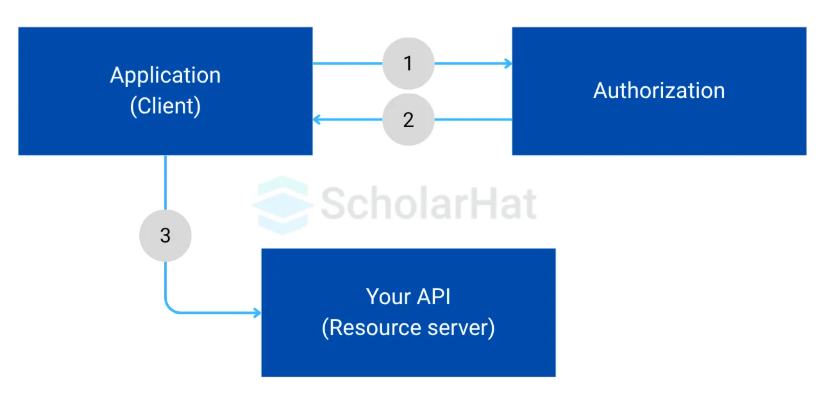
- The Application (Client) sends login credentials (username/password) to the Authorization Server.
- Example: A user logging in with email + password.
- The Authorization Server verifies the credentials.
- If valid, it generates a JWT (JSON Web Token) containing user details (like id, role, expiry) and sends it back to the Client.
- Now the client has a "key" to access protected APIs.
- The Application (Client) calls Your API (Resource Server), but this time it attaches the JWT in the Authorization Header: Authorization: Bearer <jwt_token>
- The API (Resource Server) validates the JWT (checks signature + expiry).
- If valid → API gives access to the requested resource (like profile info, blog data, etc.).
34. What is elasticity in architecture?
Elasticity in Architecture refers to the ability of a system or application to automatically scale resources up or down based on demand. It is a key concept in cloud computing and scalable software architectures.
- Dynamic Scaling: The system can increase resources (CPU, memory, storage) during high load and decrease them when demand drops.
- Cost Efficiency: By allocating resources only when needed, elasticity reduces operational costs.
- Performance & Reliability: Ensures the application remains responsive and available even under sudden traffic spikes.
35. What are JVM class loaders?
JVM Class Loaders are components of the Java Virtual Machine responsible for dynamically loading Java classes into memory at runtime. They allow Java programs to locate, load, and link classes as needed, rather than all at once.
36. Difference Hibernate vs. JPA.
| Features | Hibernate | JPA(Java Persistence API) |
| Type | ORM (Object-Relational Mapping) Framework | Specification/interface for ORM in Java |
| Implementation | Provides its own implementation | Standard API; needs an implementation (like Hibernate) |
| Portability | Less portable, tied to Hibernate | More portable across different ORM providers |
| Query Language | HQL (Hibernate Query Language) + native SQL | JPQL (Java Persistence Query Language) + native SQL |
| Vendor Lock | Tightly coupled if you use Hibernate-specific features; switching becomes harder. | Reduces vendor lock-in, since you can switch providers (Hibernate, EclipseLink, OpenJPA) by changing configuration. |
| Functionality | Provides all JPA features + advanced features like caching mechanisms, Hibernate Query Language (HQL), multi-tenancy, custom types, etc. | Offers basic operations like CRUD, query language (JPQL), entity lifecycle, caching specification. |
| Use Case | When advanced ORM features beyond JPA are needed | When portability and standard compliance are required |
37. What is Garbage Collection?
Garbage Collection in Java is the automatic process of reclaiming memory by removing unreachable objects from the heap, ensuring efficient memory management without manual intervention.
Unlike languages like C/C++, Java developers don’t need to manually allocate or free memory, the Garbage Collector (GC) runs in the background and reclaims memory for unused objects. Objects become eligible for garbage collection when no live thread can access them.
38. What is Docker in Java context?
Docker is a containerization platform that allows you to package a Java application along with all its dependencies (JDK, libraries, configuration, runtime environment) into a lightweight, portable container.
In the Java context, Docker ensures that your application runs consistently across different environments like development, testing, or production.
39. Explain RESTful principles.
REST (Representational State Transfer) is an architectural style for designing networked applications, often used in Java web services. RESTful APIs follow these key principles:
- Each request from a client must contain all the information needed to process it (e.g., authentication, data).
- The server does not store client session state.
- The client (UI/front-end) and the server (data/back-end) are independent.
- This improves scalability and flexibility (front-end and back-end can evolve separately).
- A consistent way of interacting with resources using standard HTTP methods:
- Resources are identified using URIs (e.g., /users/101).
- Everything is treated as a resource, represented by URIs.
- Resources can have multiple representations (JSON, XML, etc.).
- Resources are transferred in standard formats like JSON or XML.
- REST allows multiple layers (e.g., security, caching, load balancing) without the client needing to know about them.
- Responses should define whether they are cacheable or not to improve performance.
40. What are JVM class loaders?
- It loads the core Java classes from the JDK (e.g., java.lang.*, java.util.*).
- It is part of the native JVM code and does not have a parent.
- It loads classes from the jre/lib/ext directory or from java.ext.dirs.
- Example: optional libraries or extensions.
- It loads classes from the classpath (e.g., your project’s /bin, target/classes, or external JARs).
- Most of your application classes are loaded by this loader.
- Developers can create their own class loaders by extending ClassLoader class.
- It is useful for loading classes dynamically from non-standard sources (like network or encrypted files
41. How do you resolve a disagreement with a coworker regarding your use of a Java system?
Conflict resolution is a critical ability for a Java architect. By describing the behavioral method you would use to deal with this circumstance, you can demonstrate to a recruiter that you can work well in a team. Additionally, you might utilize your response to demonstrate your aptitude for a future leadership post. This is a common technical architect interview question to understand behavioural skills.
To better serve my coworkers’ needs, I’d consult my schooling and job expertise in Java, as well as online Java resources and the Oracle support system. I’d notify my boss or team leader right away about my coworker’s resistance and seek guidance on addressing the matter.
42. Explain the CAP theorem in the context of Java-based distributed systems.
- Consistency (C) – Every read receives the most recent write or an error.
- Availability (A) – Every request receives a response (success or failure), without guarantee of the latest write.
- Partition Tolerance (P) – The system continues to operate despite network failures between nodes.
Distributed Java applications often use microservices with databases like Cassandra, MongoDB, or PostgreSQL clusters. In Java distributed apps, Partition Tolerance is a must, so architects choose between Consistency and Availability based on business needs.
43. How do you design for high availability in Java-based systems?
For Designing High Availability Design in Java Systems follow this:
- Stateless Services: It ensures services do not maintain state; store session externally (e.g., Redis).
- Load Balancing: Distribute traffic across multiple service instances (Nginx, HAProxy, ELB).
- Redundancy & Clustering: Deploy multiple service instances and replicate databases.
- Failover Strategies: Automatic recovery for service or database failures.
- Resilience Patterns: Use circuit breakers, retries with backoff, and bulkheads.
- Monitoring & Alerting: Track service health with Prometheus, Grafana, ELK/EFK stack.
- Cloud/Infrastructure: Deploy across multiple availability zones, use auto-scaling, and consider serverless components.
44. What strategies do you use for database scaling in Java applications?
Vertical Scaling (Scale Up)
- Increase the resources of a single database server, such as CPU, RAM, and SSD.
- This is simple but limited by the hardware capacity.
Horizontal Scaling (Scale Out)
- Distribute data across multiple database instances using sharding or partitioning.
- This approach is ideal for large-scale applications with heavy traffic or big data.
Replication
- Set up primary (master) and secondary (slave/replica) nodes.
- The primary handles writes, while replicas manage reads, which improves performance and fault tolerance.
Caching
- Store frequently accessed data in memory using Redis or Memcached.
- This reduces the database load and speeds up responses.
Optimized Database Access
- Use connection pooling with HikariCP to manage database connections efficiently.
- Optimize ORM queries with Hibernate or JPA by using lazy loading, batch fetching, and query tuning.
Database Selection / Polyglot Persistence
- Choose SQL for structured transactional data or NoSQL for distributed, high-volume workloads.
- Make sure the database type fits your needs for consistency, availability, and performance.
45. How do you manage configuration in distributed Java systems?
46. What are the main differences between SOAP and REST in Java services?
| Feature | SOAP | REST |
| Definition | Protocol for exchanging structured information in web services using XML. | Architectural style that uses HTTP for communication and resource manipulation. |
| Message Format | Strictly XML; message structure defined by WSDL. | Flexible: usually JSON or XML; no strict message format. |
| Transport Protocol | Can use HTTP, SMTP, TCP, or JMS. | Primarily HTTP/HTTPS. |
| State Management | Can maintain state (stateful), but also supports stateless. | Stateless by design; each request contains all necessary info. |
| Security | Built-in standards: WS-Security, digital signatures, encryption. | Relies on transport-level security like HTTPS, OAuth, JWT. |
| Performance | Slower due to XML parsing and overhead of SOAP headers. | Faster and lightweight; smaller payloads. |
| Complexity | More complex; requires strict contracts via WSDL. | Simpler and easier to implement; no formal contract needed. |
| Use Cases | Enterprise applications needing reliability, ACID transactions, and strict security. | Web, mobile, and microservices needing scalability and lightweight communication. |
47. How do you implement caching in large-scale Java applications?
In large-scale Java applications, caching boosts performance by storing frequently accessed data in in-memory caches (Caffeine, Ehcache) or distributed caches (Redis, Hazelcast).
48. How do you design fault-tolerant Java microservices?
Fault-tolerant Java microservices use circuit breakers, retries, bulkheads, failover, asynchronous messaging, timeouts, and monitoring to prevent cascading failures and ensure service continuity.
- Circuit Breakers:Use libraries like Resilience4j or Hystrix to prevent cascading failures.Automatically stops calls to failing services and provides fallback responses.
- Retries with Backoff:Retry transient failures with exponential backoff to avoid overwhelming services.
- Bulkheads: Isolate different service components to prevent one failing service from affecting others.
- Failover & Redundancy: Deploy multiple service instances across different servers or availability zones. Use load balancers (Nginx, ELB) for automatic failover.
- Asynchronous Messaging: Use message queues or event streaming (Kafka, RabbitMQ) to decouple services and handle spikes.
- Timeouts and Graceful Degradation: Define timeouts for service calls to avoid long waits. Provide degraded but functional responses when a service fails.
- Monitoring & Alerts: Use Prometheus, Grafana, ELK for real-time monitoring. Set up alerts for early detection of failures.
49. What is your approach to DevOps and CI/CD for Java applications?
DevOps & CI/CD Approach for Java Applications
- Use Git for source code management.
- Follow branching strategies like GitFlow or trunk-based development.
- Use Maven or Gradle to manage dependencies and build artifacts.
- Automate builds for reproducibility and consistency.
- Use tools like Jenkins, GitHub Actions, or GitLab CI.
- Automatically run unit tests, code quality checks, and static analysis on each commit.
- Automate deployment pipelines to staging and production environments.
- Deploy containerized applications using Docker and orchestrate with Kubernetes.
- Integrate unit, integration, and end-to-end tests.
- Use SonarQube or similar tools for code quality, linting, and security checks.
50. How do you integrate AI/ML services into Java enterprise applications?
- Utilize APIs from AWS SageMaker, Google AI Platform, Azure Cognitive Services.
- Java SDKs allow easy integration for predictions, NLP, image recognition, and more.
- Wrap ML models in REST/gRPC services using Spring Boot or Jakarta EE.
- This decouples AI/ML logic from the main application.
- Use Kafka, Spark, or Flink for processing large datasets asynchronously.
- Suitable for real-time recommendations or fraud detection.
- Maintain a feature store to manage input data consistently across training and production.
- Use libraries like Apache Commons, Deeplearning4j, or ND4J for preprocessing in Java.
- Track model versions, performance metrics, and data drift.
- Tools: MLflow, DVC, or cloud-native monitoring.
- Connect ML services with Java enterprise apps via APIs or message queues.
- Ensure proper error handling, logging, and fallback mechanisms if predictions fail.
Conclusion:
Preparing for a Java Technical Architect interview requires a combination of deep Java expertise, architectural vision, and knowledge of modern enterprise practices. From understanding core Java concepts and design patterns to designing scalable, fault-tolerant microservices and integrating cloud, DevOps, and AI/ML solutions, a successful architect demonstrates both technical mastery and strategic thinking.
Enroll in ScholarHat's Java Solution Architect Certification Training with hands-on, work experience-based learning for building real world projects.





 LEAD-ACE: EdTech Platform
LEAD-ACE: EdTech Platform